- Posted By Peter Hottinger, CCO of QFI Risk Solutions, Ltd
- On 31 Mar, 2025
- Category : Company Blog
Discover how to integrate continuous cyber security monitoring with GDPR and NIST compliance requirements to protect your organization from evolving threats.
Table of Contents
Open Table of Contents
The Intersection of Cyber Risk and Compliance
Cybersecurity has evolved beyond an IT concern to become a critical business function affecting every department. The rapid acceleration of cyber threats and increasingly stringent regulatory requirements have forced organizations to reconsider their approach to security risk management.
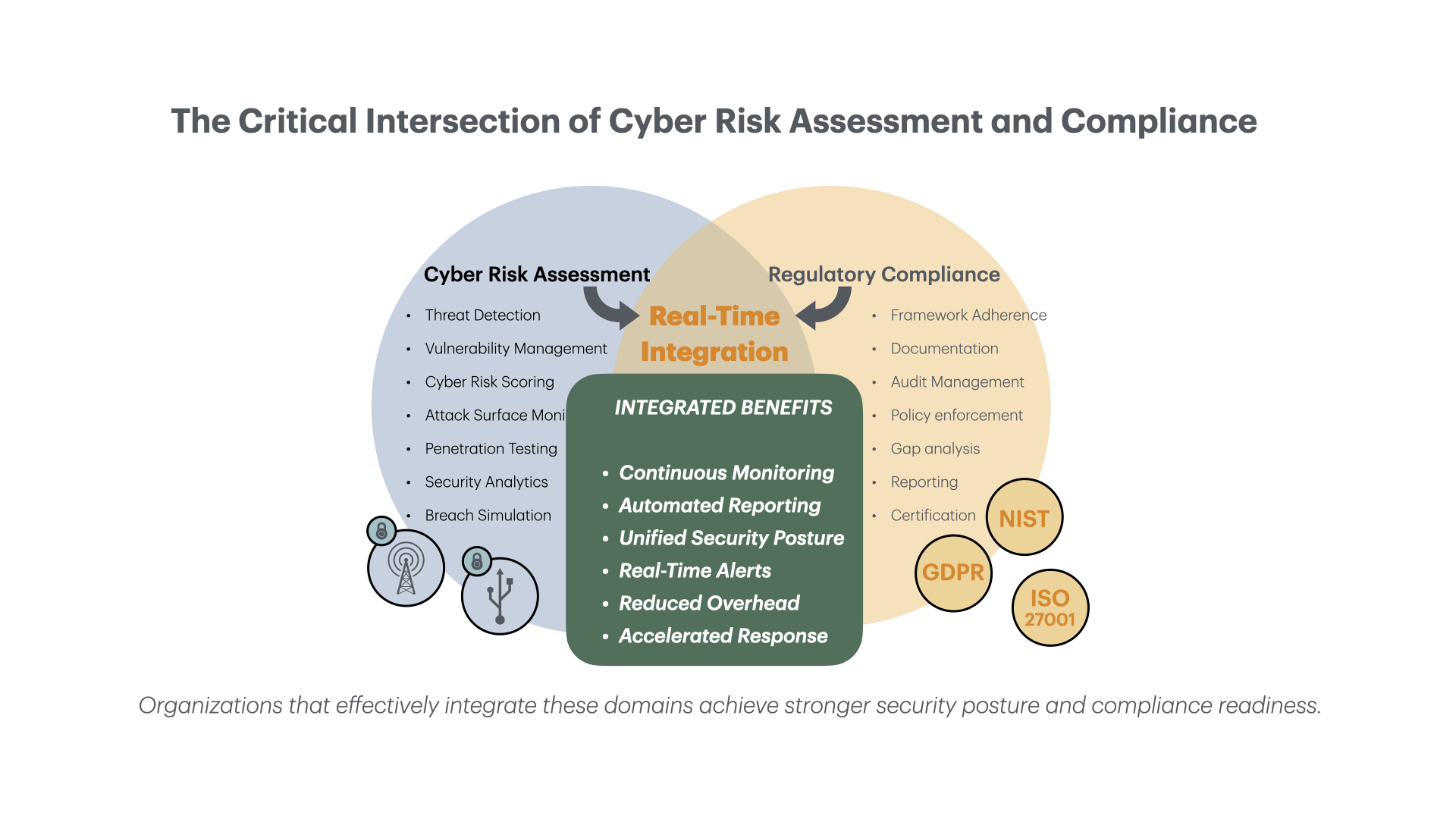
Regulatory frameworks such as GDPR, NIST, and other compliance standards mandate comprehensive security measures, challenging businesses to balance proactive risk evaluation with strict compliance obligations.
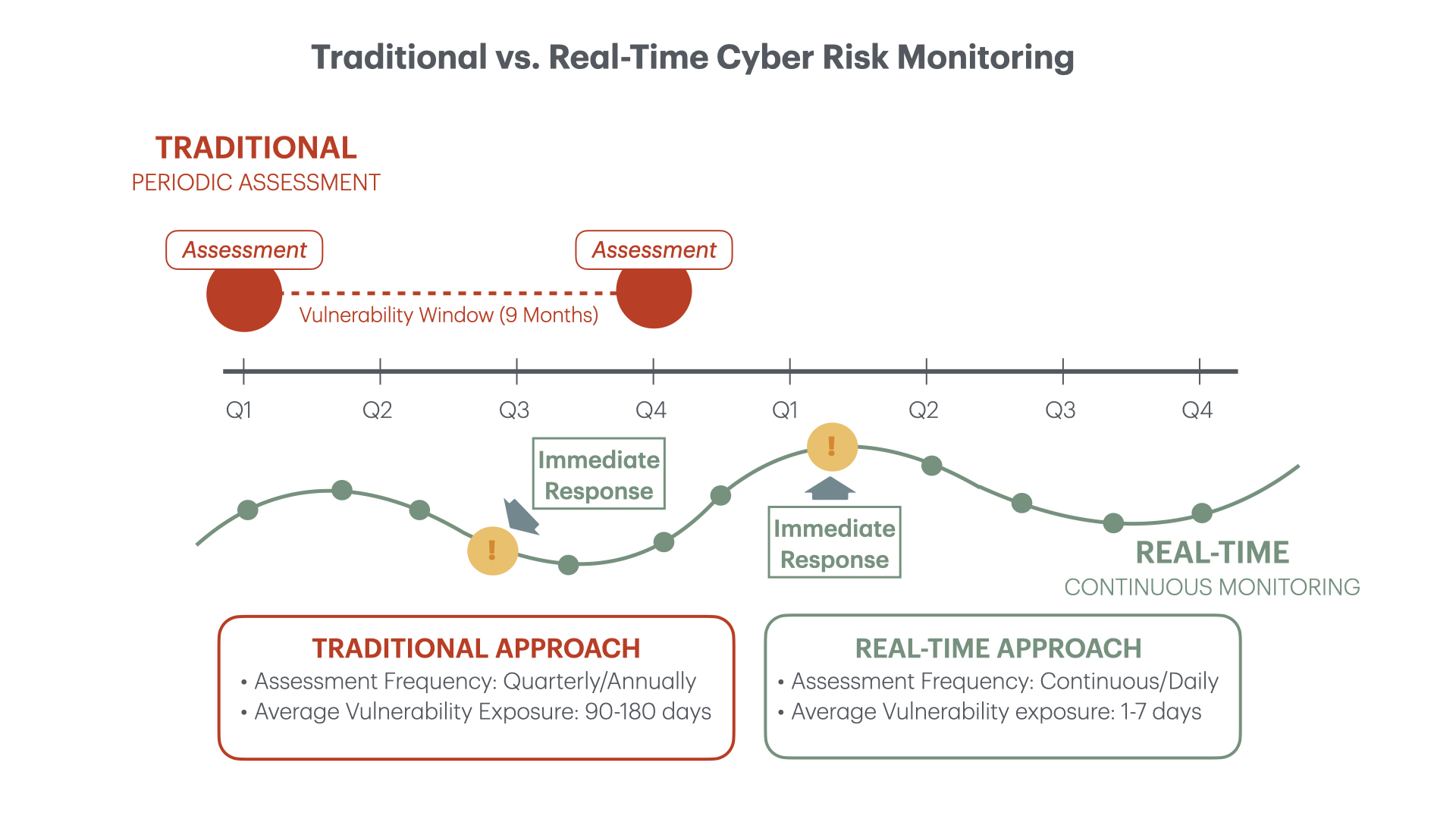
Many organizations struggle with integrating real-time cyber risk assessments with regulatory compliance needs. Traditional periodic evaluations fail to address today’s dynamic threat landscape. Forward-thinking businesses are now implementing continuous security monitoring strategies to ensure compliance while mitigating cyber risks before they escalate into costly data breaches.
Why Real-Time Cyber Risk Assessments Matter
Cyber risks evolve constantly, making continuous security monitoring essential for proactive protection. Organizations can no longer rely on quarterly or annual security reviews—they need real-time vulnerability detection to identify and neutralize threats as they emerge.
Key Benefits of Continuous Security Monitoring:
- Faster Threat Detection and Response: Identify vulnerabilities and cyber threats in real-time, enabling immediate remediation before breaches occur
- Ongoing Compliance Verification: Maintain an up-to-date security posture by continuously identifying and addressing compliance gaps
- Minimized Non-Compliance Risk: Active monitoring helps organizations stay aligned with regulatory requirements, reducing the risk of penalties and legal consequences
- Enhanced Security Posture: Continuous assessment strengthens overall defenses against emerging attack vectors
As threat actors deploy increasingly sophisticated methods, businesses must integrate real-time risk management into their cybersecurity strategies to maintain regulatory compliance and protect sensitive data from compromise.
Key Regulatory Frameworks
Understanding how regulatory frameworks impact your cybersecurity compliance requirements is essential for creating an effective security program that satisfies both business and legal needs.
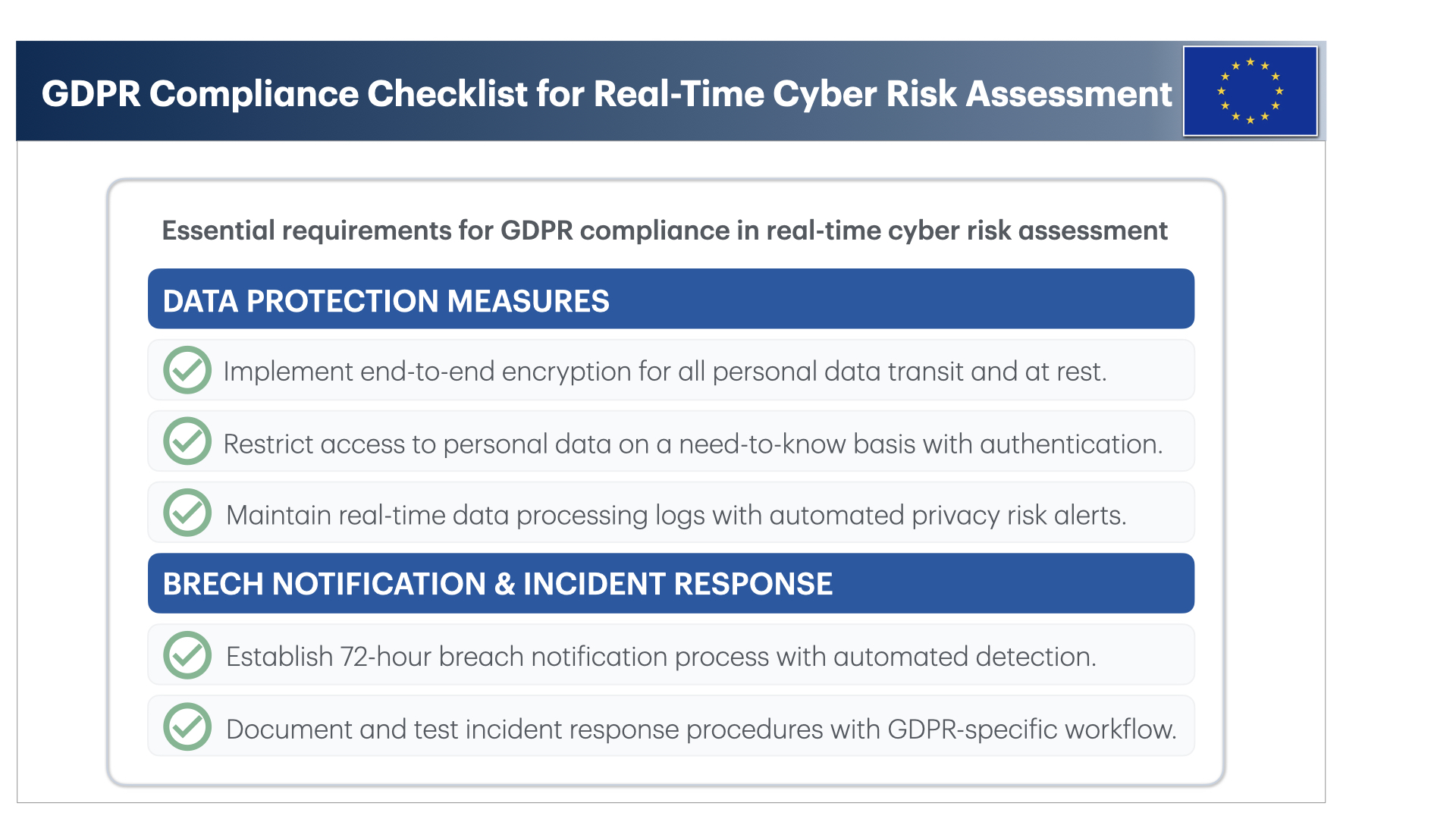
GDPR Compliance Requirements
The General Data Protection Regulation (GDPR) establishes strict data protection standards, requiring organizations to safeguard personal information and report breaches within 72 hours. To achieve GDPR compliance, organizations must:
- Conduct regular Data Protection Impact Assessments (DPIA) to identify and mitigate privacy risks
- Implement strong encryption and pseudonymization techniques to enhance data security
- Maintain real-time incident response capabilities to ensure timely breach notification
- Document all data processing activities and security measures
By integrating continuous security monitoring with GDPR requirements, organizations strengthen data protection controls and significantly reduce the likelihood of facing non-compliance penalties that can reach up to 4% of annual global revenue.
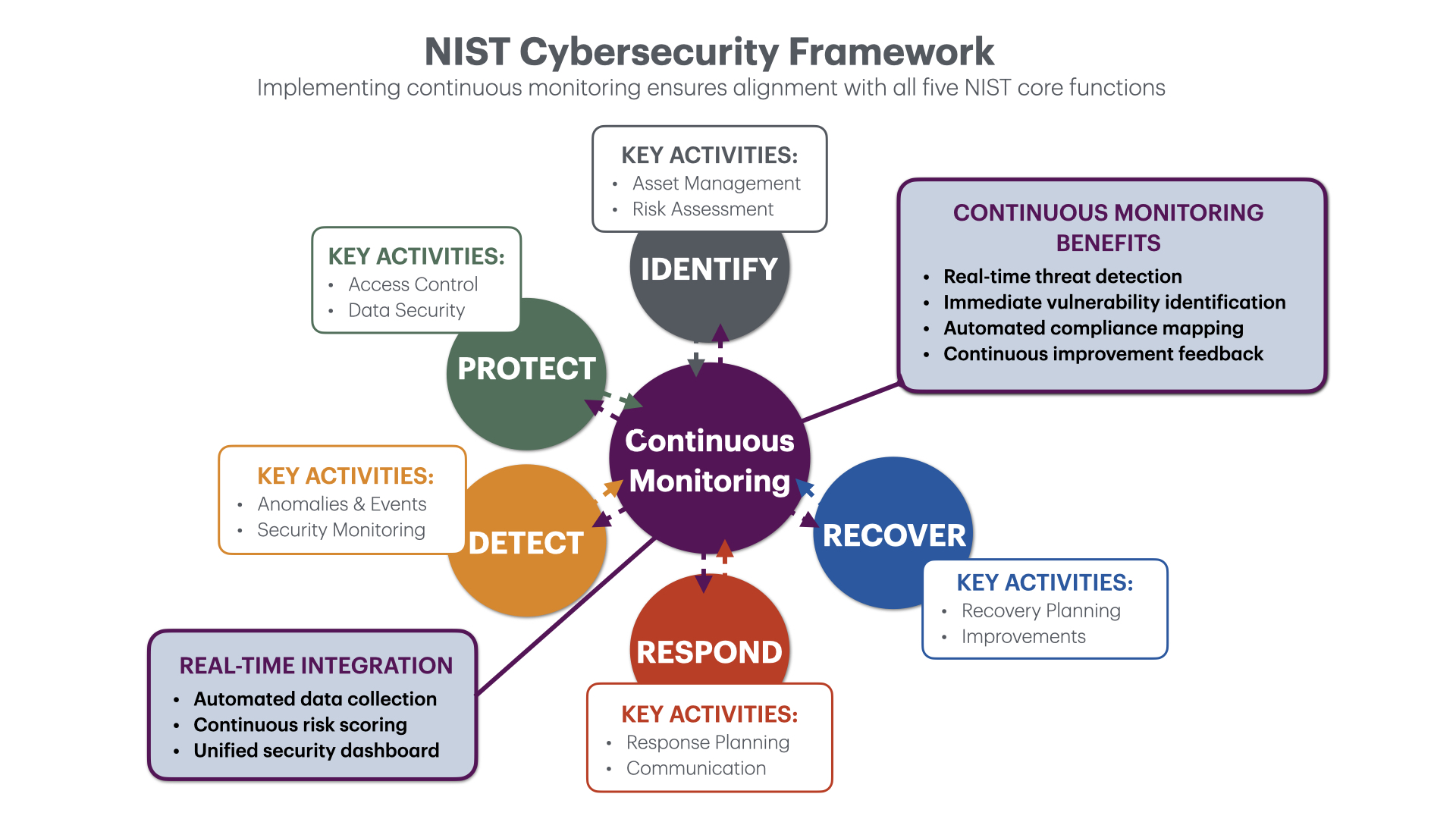
NIST Cybersecurity Framework Implementation
The National Institute of Standards and Technology (NIST) provides a structured approach to cybersecurity risk management through its five core functions: Identify, Protect, Detect, Respond, and Recover. Real-time security assessment aligns perfectly with NIST’s emphasis on continuous monitoring, enabling organizations to:
- Identify vulnerabilities before they escalate into major security incidents
- Detect and respond to suspicious activities promptly
- Maintain ongoing compliance through automated security assessments
- Create a resilient security architecture that adapts to new threats
Organizations implementing real-time risk management tools ensure continuous alignment with NIST’s cybersecurity framework, enhancing both security effectiveness and compliance efforts.
Automating Compliance Reporting
Compliance documentation is typically time-consuming and complex. Automating compliance workflows allows organizations to streamline reporting, minimize human error, and stay current with evolving regulations.
Benefits of Automated Compliance Solutions:
- Real-Time Data Collection: Continuous monitoring ensures compliance-related data is automatically gathered and analyzed without manual intervention
- Instant Alert Notifications: Automated warnings help security teams address potential violations before they result in non-compliance findings
- Regulatory Update Integration: Ensures security policies remain aligned with the latest compliance standards as they evolve
- Continuous Audit Readiness: Maintains detailed, timestamped records of compliance activities, facilitating seamless audits and regulatory reviews
According to a recent study by the Ponemon Institute, organizations using automated compliance tools reduce audit preparation time by up to 70% while improving accuracy by 85%.
4 Proven Strategies for Alignment
To bridge the gap between cyber risk management and regulatory compliance, implement these strategic, integrated approaches:
1. Integrate Risk Assessment Tools with Compliance Frameworks
Many organizations rely on separate tools for security risk evaluations and compliance reporting, creating inefficiencies and potential blind spots. Businesses can streamline cybersecurity operations while ensuring regulatory alignment by implementing unified risk management platforms that automatically map security findings to specific compliance requirements.
Implementation tip: Look for solutions offering pre-built compliance templates for frameworks like GDPR, NIST, ISO 27001, and PCI DSS.
2. Implement Continuous Monitoring and Auditing
Compliance isn’t a one-time achievement but an ongoing process requiring persistent vigilance. Establish real-time security auditing mechanisms to identify emerging threats and continuously assess regulatory adherence. This approach ensures security gaps are promptly addressed, substantially reducing the risk of non-compliance findings.
Case study: A financial services firm implementing continuous compliance monitoring reduced security incidents by 45% and cut audit preparation costs by 60% within 12 months.
3. Leverage Automation for Risk Mitigation
Automated security solutions—including vulnerability scanning, patch management, and AI-driven threat intelligence—provide organizations with real-time insights into cyber risks without overwhelming security teams. These tools enhance compliance by reducing manual intervention and ensuring continuous regulatory alignment even as threats evolve.
4. Strengthen Cybersecurity Awareness Across Departments
Regulatory compliance and cyber risk management require unified effort across all organizational functions. Implement ongoing security awareness training to ensure employees understand compliance requirements and their role in maintaining a secure environment.
Best practice: Create role-specific training that addresses the unique compliance responsibilities of different departments, from IT to HR to finance.
Next Steps for Your Organization
As cyber threats evolve in sophistication and frequency, organizations must prioritize real-time risk management and align security efforts with regulatory frameworks like GDPR and NIST. Integrating automated compliance reporting and continuous monitoring ensures your business remains compliant while proactively mitigating cyber risks.
Cybersecurity compliance extends beyond meeting regulatory requirements—it’s about building a resilient security framework that safeguards organizational assets and customer trust. By adopting a proactive, data-driven approach to compliance, your organization can effectively bridge the gap between real-time risk assessments and regulatory alignment.
Ready to strengthen your organization’s compliance posture? Contact our cybersecurity experts today for a complimentary risk assessment and discover how our real-time monitoring solutions can help you achieve continuous compliance.